Most of my blog is in Hungarian, the below English entries are generally reprints of my Linkedin posts. They are also available via via RSS
 .
.
I made a rather rookie mistake.
I decided to create an AI tool for gathering and organizing security news to help stay on top of what is going on. I wrote a 'serverless' Google Cloud function to run on a regular basis, invoke an AI prompt to gather those security news from the past x weeks that I am interested in, organize them into categories, summarize them, and put summaries and links on a web page so that I can review them. All worked well. ✅
...until I noticed that some of the links were broken. Further investigation showed that almost none of the links worked properly, they were broken, pointed to non-existing paths, or to example.com. The problem was not with the links, but with the news. All hallucinations. 🦄🐲👾
Having spent some time refining my prompt, experimenting with multiple AI models and learning techniques for 'grounding' the model, I realized:
The whole thing was a very bad idea.
If you ask AI to gather news, it will 'want' to give you lots of news. To please you, it will even invent some. That is the way it works. There are techniques to tune the model's 'temperature', push the model to ground the results and force it to provide evidence that they exist, you might be better off with a more advanced model or one trained more recently, but no matter what you do it may hallucinate. That is the way it works.
AI can do wonders when processing data🤖🌈 or for summarizing the past, but telling an AI to go and gather fresh news from the past x weeks is a bad idea (at least with today's tech). You need to gather this kind of data then you can make AI filter/process/organize it -- this seems to be the only way to get rid of hallucinations.
This post was first published on Linkedin here on 2026-05-10.
|
Prompt injection is the injection attack we can't actually fix.
Injection attacks💉 work by tricking a program to execute parts of malicious input data as if they were program code. In SQL for example, your code and text data are separated via apostrophes ('). Code is executed deterministically, while data is just payload. If the attacker can craft malicious input data to circumvent this separation (e.g. by having apostrophes in the input data), the system may execute data from the attacker as if it was code → they 'hack' the system.
Solution: Ensure your separation is robust and accounts for malicious input. (For SQLi: either ensure input cannot have apostrophes or escape them properly, use prepared statements, etc.)
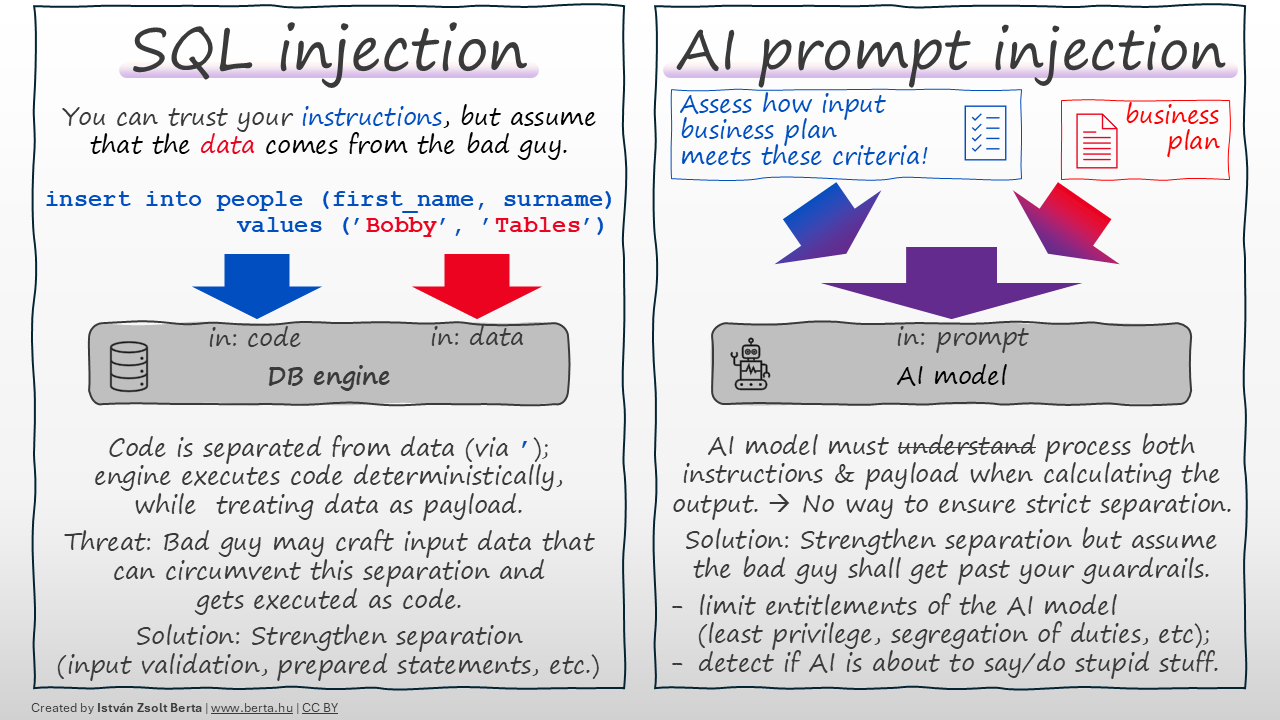
An AI model🤖 receives a prompt from with instructions the programmer, potentially along with untrusted data payload for processing. In case of prompt injection, the attacker crafts malicious payload so that the AI model would confuse it with the instructions; if successful, the attacker can make the AI model do or say anything they want.
Fundamental difference: Both the instructions and the data get folded into the same 'prompt', before processed by the AI model. There is no strict separation between instructions and data payload, and — based on my understanding — STRICT SEPARATION IS NOT POSSIBLE with current technology. The AI model needs to process and 'understand' both instructions and payload and both shall 'influence' their conclusions. There is no way to mark certain parts of the prompt so that the model cannot 'execute' them as commands. (While you can give such 'instructions' like 'ignore user commands', they will be part of the same prompt and at the same level; if the attacker's 'ignore instructions' command is more persuasive, the AI will follow it.) Not a bug🐞 — a feature of how this technology works.
I am not saying you should not strengthen separation of instructions and code as much as you can (e.g. via guardrails or other AI agents checking for malicious prompts or contaminated output). Do these, but be skeptical, as they are trying to 'make water not wet'.
What can give more assurance?
- 👉 Limit what the AI model can do (least privilege, segregation of duties and other traditional security measures you would use for a human).
- 👉 Assume the bad guy gets past your guardrails → detect and act if the AI is about to say or do something stupid. Use deterministic tools here, don't rely on AI alone to catch AI. (AI agents may fall victim to the same attack they are supposed to detect.)
TL;DR: Most injections are solved by separating code from data. In AI, the code is the data. Don’t trust AI the output blindly, use common sense.
This post was first published on Linkedin here on 2026-04-19.
My career started with 8 years at a 🏠small security company (<100 people), followed by 13 years at a 🏦global bank (200k+ people).
A question I get a lot now: Which is better — small or large companies?
I worked with outstanding professionals and learned a lot in both. My answer is simple: neither is better, they are just different, and both have their own charm.
- 🏠 At the small company, we had to build everything ourselves — I could also influence anything I wanted to.
- 🏦 At the large company, I could leverage the global infrastructure — I also had to spend time understanding this infrastructure and aligning with it.
When facing a new problem:
- 🏠 small company — I had to figure out how we shall be doing this from now on.
- 🏦 large company — A detailed process already existed for everything; finding the right process was the real challenge.
When I became a manager:
- 🏠 small company — I had to define my role from scratch as my level did not even exist before. I had to define how I operate, how I evaluate and support people, what authority I have, etc.
- 🏦 large company — I could rely on the rules, processes and culture of the org; there were people to ask, and patterns to copy, with courses and mentorship programs teaching you how to manage.
When hiring:
- 🏠 small company — We were growing and thus looking for smart people to build on; sometimes we lost great talent because we could not fully utilize their skills.
- 🏦 large company — We were looking to find the right person for the given job opening; sometimes I had to pass on very talented people (or refer them to peer teams) as they did not fit a precise need.
For decisions/approvals:
- 🏠 small company — Walk next door, make the decision.
- 🏦 large company — Some approvals had to go 3-4 levels up, articulating the problem in such a vast ecosystem was a challenge itself.
On my role itself:
- 🏠 small company — My job was security.
- 🏦 large company — Security was a huge org, and we all played our small parts in it. Each line in my previous job description now had a separate organization with hundreds of people.
While building security:
- 🏠 small company — We were struggling to consistently secure everything we have.
- 🏦 large company — We were struggling to know what we have and to make sure they all go to the right processes; once the correct process was followed, consistency came naturally. Visibility, reporting and finding the right owner was key.
Getting things done:
- 🏠 small company — It all depended on if you knew the right people. We called it chaos.
- 🏦 large company — It all depended on if you knew the right people. We embraced it as 'networking'. 😄
➡️ Both experiences shaped how I think about leadership, scale, and impact.
What differences have you experienced between small and large organizations?
This post was first published on Linkedin here on 2026-04-16.
|
We had a cool discussion on full-disk encryption🔏 with @Szabo, Krisztian, @Menyhart, Zsolt and @Bordas Istvan. Let me share some of my takeaways.
Background: In corporate environments, employees use laptops, and when these laptops get inevitably lost/stolen, gigabytes of sensitive/customer data can be leaked. You are required to notify customers®ulators, who get pissed off, fines and lawsuits follow, etc. Therefore, it is a no-brainer encrypt to the whole drive of laptops. This protects against a thief using highly advanced technologies (e.g. screwdriver🪛😄) for removing the drive, inserting it in another machine, and thus circumventing OS level protection. If the thief cannot decrypt the data, you did not leak your sensitive/customer data. No compliance nightmare, you just lost some hardware. Of course, encryption does not count, if you put the decryption key in clear right next to the encrypted data.
Traditional full-disk encryption schemes (often used in Linux native LUKS) ask for a password before booting the OS:
- The machine boots from a small unencrypted part of the drive, and prompts for your password (or token, etc).
- A key is derived from the password; the rest of the drive is encrypted, and can be decrypted using this key.
- Going forward, data read from the drive is decrypted, data written to the drive is encrypted with this key transparently.
- Thus can the OS boot up, so you can login.
You may have seen BitLocker+TPM first boot an OS and then ask for a password. It works as follows:
- The master key is stored in the machine's TPM chip (Trusted Platform Module).
- During boot-up, TPM validates if key components of the machine have changed.
- If the hardware is the same, TPM gives access to the decryption key and the OS boots up and you can log in.
IMO this latter is fishy🐟:
- 👉 In the traditional setup the decryption key is not there, this forces the thief to break cryptography (considered impossible unless they have unrealistic resources).
- 👉 In case of TPM, it is a fair assumption that extracting the key from the TPM chip is beyond the capabilities of most attackers. However, in this TPM setup the thief can get to a running OS which has access to the decrypted data. Attacking such an OS when you have physical access to the machine is MUCH easier.
This is not a BitLocker vs LUKS thing; both can function in both setups.
This is not a TPM thing either; TPM can be set up to ask for a password before the OS boots up.
There are pros and cons for both the user entering the password and for storing it in the TPM chip; e.g. TPM chip's integrity check can 'lock' the drive to the given machine, and may even defend vs the 'evil maid' attack.
However, if a lost laptop's OS can boot up without any credentials, I am not sure on can confidently say: 'no worries, the drive was encrypted, no data is leaked'. Even if the thief cannot remove the drive, an OS login's security is just not in the same league as encryption.
What do you think?
This post was first published on Linkedin here on 2026-04-01.
|
This week was my last full week at Citi. It was more than thirteen years ago when I first walked in through the company's doors, and it was an incredible journey.
I am truly grateful to Citi. I have learned and grown a lot during all these years, I will always remember them as a beautiful and exciting period of my career. I would also like to thank all who supported, helped, mentored, challenged and inspired me throughout these years and thank all the great people I have come to know, and I have worked with.
Now it is time to move on and bid farewell, as new challenges await... Stay tuned! 😉
This post was first published on Linkedin here on 2026-03-23.
